The average cost of a data breach in 2019 was around $4 million per company. It was a record year, further demonstrating the growing problem of data breaches. What’s even more disturbing, these figures don’t include mega breaches that happened at Capital One, Equifax, Marriott, and other newsworthy attacks.
But your company doesn’t have to be a victim. You can avoid data breaches. Read on to discover the most common causes of data breaches and what companies can do to prevent them from happening.
Why do Data Breaches happen? 7 Common Causes
1) Unpatched Software
Billions of people use Windows daily. Hundreds of millions use Facebook, Instagram, YouTube, and other forms of social media. Tens of millions use apps, play games, and do other things either on their computer or smartphone.
Hackers are targeting these critical features of everyday life. They exploit vulnerabilities to gain access to personal data. Reputable developers work hard to prevent hacks from happening. But if you don’t upgrade or patch your software, it’s like giving fraudsters a free pass to steal your data.
2) Social Engineering
In social engineering attacks, cyber criminals convince you to divulge your sensitive information, including login credentials. They use a variety of tactics. In some cases, they may use spoofing to pretend to be a known contact, such as a company you do business with.
They may ask for a payment or something innocuous like a previous invoice statement for accounting records. Then they use the information to gain access to your network or your business accounts.
3) Human Error
Sometimes you can do everything right, but one small mistake can leave your entire company susceptible to a significant data breach. It is the most frustrating thing about data security. Human error accounts for over 50 % of all security breaches. Errors may vary, but familiar scenarios include:
- Sharing information with the wrong recipients
- Using weak passwords
- Clicking on infected files or links
- Sharing account information
- Leaving important files unencrypted
4) Network Attack
Network attacks tend to be more sophisticated. Cyber criminals use systems or infrastructure weaknesses to break into the network. In some cases, they use social engineering. They also may take advantage of unsecured network protocols to monitor network activity and gain access. Whatever way they gain access, it puts your entire company at risk.
5) Malware
Malware is everywhere on the internet. This threat is expanding and harms both personal and business devices. According to Verizon, five malware events happen every second. While most are minor, there is an incredible amount of malware variation.
Even if your computer can protect against 99.99% of malware, it’s only a matter of time until one may get past your antivirus software.
- Related: 6 Effective Ways to repair a Malware damaged PC
- How to remove malware from computer with a free tool
Hint: We suggest you to use Malwarebytes(25% Discount Link) to protect your PC from Malware.
6) Insider Misuse
Human error implies an innocent mistake. But some people may deliberately misuse authorized entry for personal gain. It can be challenging to catch insider abuse. You can also not notice these events for an extended amount of time.
In many examples, companies discover insider misuse during an examination of user devices after employees leave the company. For this reason, even with trusted employees, routine audits may be necessary. It’s the only way to make sure nothing suspicious is happening.
7) Physical Theft or Network Infiltration
Although most threats are digital, severe issues also exist in the real world. Thefts of laptops, smartphones, USB drives, and servers represent a severe security risk.
Thefts can occur both in the work environment, at home, and in other locations. When these happen, you can never be sure whether it’s an opportunistic event or something more malicious in nature. In both cases, if fraudsters penetrate a device, your company data is at risk.
How to Protect Your Business from Data Breaches
Data security begins at the top. All companies, regardless of industry or size, need to have a strict cybersecurity policy. You can diminish the risk of a data breach by doing the following:
- Educate employees on the importance of digital hygiene. Enforce using strong passwords, MFA, updating all devices and apps, and so on. Be sure to encourage open discussion of suspicious activity. The sooner you catch a threat, the less damage it can do.
- Use a business VPN to protect network connections. Options like NordVPNLayer also help you to manage access to online platforms for remote workers. If you are an individual, you can use NordVPN(70% Discounted link) instead of NordLayer.
- Enable the latest antivirus software from Avast(20% Discounted Link), Norton(Special Discounted Link), or Malwarebytes(25% Discounted Link).
- Restrict user permissions to only what’s necessary to perform work responsibilities.
- Audit all visitors both physically in your building along with those who have guest network access.
Use ManageEngine Endpoint Central

ManageEngine Endpoint Central is a cutting-edge Unified Endpoint Management and Security (UEMS) solution designed to streamline and safeguard the modern-day digital workspace distributed across different device types and operating systems. The solution employs a single lightweight agent, providing comprehensive device lifecycle management and robust security functionalities like real-time threat detection and containment mechanisms.
With a wide array of features ranging from automated patching to instantaneous endpoint analytics, the solution helps minimize operational disruptions and enhance end-user experience by addressing the need for unified management of devices, applications, and data. Integrated security capabilities like next-gen antivirus, anti-ransomware, vulnerability assessment, endpoint encryption, and web filtering further help organizations enhance the overall security posture of their endpoints.
Available in both on-premises and cloud, it seamlessly integrates into existing frameworks, offering flexibility in deployment options while facilitating interoperability and smooth functionality within diverse organizational setups.
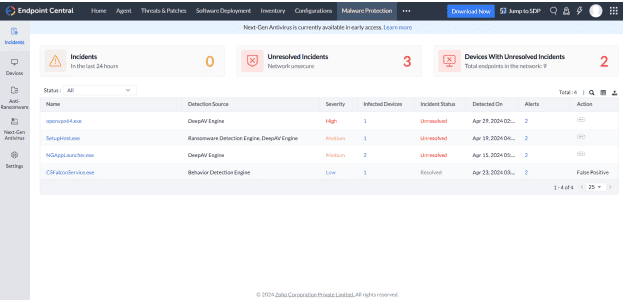
Pricing:
Endpoint Central provides flexible pricing options, starting at just $795 per year, and includes a 30-day free trial to get you started.
Cybersecurity can make or break a business. 60% of small businesses fail within six months of a data breach. Arm yourself with the latest technology and insider strategy to make sure your company isn’t one of them.
If you like this tutorial about making your workplace more Eco-friendly, please share it and follow WhatVwant on Facebook, Twitter, and YouTube for more tips.
68% NordVPN discount Coupon
Our readers get a special 68% discount on NordVPN for 2 years plan.
Why do data breaches happen?-FAQ
What is the main cause of data breach?
Weak and stolen credentials like password, Malware, Social Engineering, Human error, etc are the main cause of data breaches.
How a data breach affect the organization?
Data breach affect the organization by compromising the sensitive information.
Who is responsible for data breach?
The data owners and data holders are the main responsible for Data breaches.
How to protect the data from data breaches?
BY using a VPN services, Antivirus software and by restricting the users permission you can protect the data from data breaches.
Which is the best VPN service?
NordVPN is the best network service to protect your network connections.
