Want to learn Ethical Hacking? This tutorial will give you complete details about hacking, types of hacking, Ethical hacking, how to become a professional hacker, and the best Ethical Hacking Courses for Cybersecurity professionals through which you will become a certified hacker. We give you 10 paid and 5 free courses.
Data is the new oil that moves everything in the world. It is the single most important currency when it comes to the growth of any organization. This also makes replica watches it the most vulnerable asset of any organization as it is always under the radar of hackers and cybercriminals.
According to a recent study, “Cybercrime will affect $6 trillion annually by 2021”. The figure looks more astonishing when compared to $3 trillion from 2015. This makes information security one of the hottest fields be in right now.
The role of an ethical hacker is to understand the bugs, flaws, and loopholes in a company’s security walls and fix them. To achieve this, they have to be able to replica Breitling understand the nuances and intricacies of cybersecurity and everything that comes with it.
Cyber Security is a field that specializes in securing the digital assets of the organization. The study of cybersecurity includes training individuals with the skills of an ethical hacker. There are multiple ways to become an ethical hacker. We will discuss the top Ethical hacking course available for cybersecurity professionals.
- Read: 8 Best ways to prevent Hacking of your PC or Mac or online activity
- 7 Best ways to prevent Hacking of your Android phone
What is Hacking?
Hacking is an activity of identifying the weakness of computers and private networks to extortionate the security of computers to get unauthorized access to your replica watches UK personal and business data. Moreover, they get control over your computer and steals any confidential information, and tries to sell them on the dark web. After getting hacked. you lose control of your pc and can’t access anything. Hacking is done using many algorithms to crack the passwords and security of the computer or any other private network.
Hacker is the person who uses their computer programming skills and security systems knowledge to exploit the security system to steal unknowns personal information and data. Some use their hacking skills for good reasons like securing your systems and websites but some use their skills in the wrong way to get unauthorized access to unknown’s systems, servers, and websites to steal their confidential data.
There are a lot of methods to hack a system or website and according to the method, hackers are also classified. The various types of hackers are listed below.
- White Hat Hackers
- Black Hat Hackers
- Grey Hat Hackers
- Script Kiddies
- Green Hat Hackers
- Blue Hat Hackers
- Red Hat Hackers
- State/National Sponsored Hackers
- Hacktivist
- Whistleblower
What is Ethical Hacking
Ethical Hacking is a method of hacking that is mostly used to penetrate and test their security system legally to find the weaknesses. Ethical hackers are also known as White Hat Hackers. They use their computer skills for good things compared to evil. There are job opportunities in the IT sector for those who have skills in ethical hacking and they use penetration or pen tools to hack. They use those tools to develop counter security to defend their systems and servers from attacks.
Hackers use a set of standard tools to penetrate through the systems. Depending upon the type of server or system to test or penetrate, the tool is selected and used. But, most of the hackers start their penetration testing using Linux OS “distro” tool. As the times moved on, the Linux distro became old and professionals are preferring another tool called “Kali distro”.
Nowadays, on the internet, you can find a lot of hacking tools for free which contains a vast amount of malware. On the other hand, some of the popular tools may also contain malware. So, before using any tool for hacking, make sure that it doesn’t have any malware or any kind of code designed to hack the hackers. For this reason, professionals write their own code to develop the tools to avoid trust issues.
What do Ethical Hackers do
Ethical Hackers are professionals in the Ethical Hacking field and they use their skills for the good cause. They are certified in Ethical Hacking and they have all the authority to use hacking tools to any extent. They use their skills and techniques to crack the security systems and grabs control over Black Hat Hackers, who intend to do bad things. The main thing Ethical Hackers do is to secure their own servers and systems from attacks and being ready for counterattacks.
What is Certified Ethical Hacker
Certified Ethical Hacker (CEH) is the qualification awarded to an Ethical Hacker by conducting a test on his/her computer skills and hacking skills. This certificate is given by the EC-Council by conducting an exam. The code of the Certified Ethical Hacking exam is 312-50. It is not an easy task to become a Certified Ethical Hacker. You have to demonstrate the knowledge regarding the security of computer systems and finding the weakness of those and providing a complete document as a report. Certified Ethical Hackers have more opportunities to work under a company or organization.
What is Black Hat Hacking
Black Hat Hacking is a type of hacking method or model similar to White hat hacking (Ethical Hacking). But the intentions are different from each other. Black Hat Hacking is mostly used in the wrong way or for a bad cause like stealing sensitive information from an individual or from an organization. Hackers who use Black Hat Hacking are known as Black Hat hackers. They use their well-known computer knowledge for their own profits and gains by using them for bad intentions. They even steal the data from the bank and the funds.
Black Hat Hackers enter into other computers or servers whether it may be an individual or an organization by deploying the security systems. They stalk and steal sensitive information from those computers and sell that stolen information in the dark market for their personal growth. On the other hand, rather than selling, they blackmail the owners of that information to fulfill their demands.
The main motive of Black Hat Hackers is to steal sensitive information from industries, banks, and many others. And making profits from that stolen information.
What is Grey Hat Hacking
Grey Hat Hacking is nothing but enjoying the hacking experience by doing experiments using loopholes on a website or on a computer. Hackers using this Grey Hat Hacking comes under the group of Grey Hat Hackers. This Grey Hat Hacking is in between the White Hat(Ethical Hacking) and Black Hat Hacking. These hackers won’t use their hacking skills for a bad cause. They just find a way to hack just by using some of the weaknesses present in the systems.
Grey Hat Hackers finds the weakness present in the system and point outs it to the system owners. They use their skills for both good and bad intentions. Depending on their usage, they are classified. When a hacker hacks the systems for his/her own personal gains or needs, then they are called Grey Hat Hackers.
The main motive of a Grey Hat Hacker is to enjoy experimenting with servers and systems using its loopholes, weakness, and crack security and finds fun in hacking. They won’t try to steal or rob any kind of sensitive information from people nor help them.
What is Script Kiddies
As everyone knows that having half knowledge about any information will be very toxic and dangerous. Script Kiddies belongs to this category. They are immature and beginner hackers in the hacking field. Script Kiddies are not skilled hackers but they do hacking by using an already made tool. They hack the hacking tools and coding scripts from the other hackers and use them to hack systems, websites, and networks. The only thing, Script Kiddies do is to grab the attention of others with their beginner hacking skills.
The main thing that Script Kiddies do is hacking others systems, networks, or websites without having proper knowledge and idea regarding the process involved in hacking. The most used tool in Script Kiddle is DoS (Denial of Service) or DDoS attack (Distributed Denial of Service). The purpose of this attack is to flood the IP address by creating very huge traffic which results in crashes.
What is Green Hat Hacking
Green Hacking hacking is the method of hacking done by new learners who are not much aware of the security systems and the internal actions of the web. Hackers using this method are known as Green Hat Hackers. These are known as “Newbies” to the hacking field as they are in the earlier stages of hacking. They use their hacking skills not to harm society or the people intentionally. But in some cases, their actions turn dangerous and creates a huge impact because of a lack of knowledge on finding and fixing the error.
You may get a doubt – “Is a Green Hat Hacker is similar to Script Kiddies?”. Basically, they both look similar but definitely not. Because Script Kiddies are amateur hackers who use others hacking scripts by downloading from other sources. Whereas Gren Hat Hackers create their own hacking script and use it. This is the major difference between Script Kiddies and the Green Hat Hackers. Moreover, Green Hat Hackers learn hacking through certified educational institutions and from proper learning sources. But the Script Kiddies learn hacking by reading online articles from websites and watching YouTube videos.
What is Blue Hat Hacking
Hacking the security systems by using a penetration tool is known as Blue Hat Hacking. It is similar to Ethical Hacking (White Hat Hacking). These Blue Hat Hackers are categorized into two types. One is Revenge Seekers and the other one is Outside Security Professionals. There is no much difference between their tools and techniques, but the only difference is the purpose for which they are using.
Revenge Seekers
Hackers of this type use their hacking skills to penetrate through the security system and steal other’s confidential data or information and publish them in public media to damage the reputation. It may be of an individual, organization, institution. Moreover, after cracking into their servers or accounts, they post and send inappropriate messages, emails from those profiles to take revenge.
Outside Security Professionals
Blue Hat Hackers of this type are called by an organization or a company to test their software for any errors before releasing it into the market. They use hacking tools to check the capabilities and weakness of that software and gives report to the company. Sometimes, companies arrange the gatherings of Blue Hat Hackers to take tests on their servers and systems.
Microsoft also arranges these types of Blue Hat Hacker gatherings to test its windows programs. So, Blue Hat Hackers are also known as Blue Hat Microsoft Hackers.
What is Red Hat Hacking
The hacking method which is used against Black Hat Hackers to take down their servers is known as Red Hat Hacking. These are just like Ethical Hacking in doing good to society. Red Hat Hackers are very aggressive in attacking the hackers intended to do for a bad cause. They use extreme and illegal paths to destroy the Bad Hackers. They choose any kind of path to make good things.
Red Hat Hackers uses various tools to break down the servers of Black Hat Hackers, some of them are listed below
- Launching DDoS (Distributed Denial of Service) attacks
- Infecting the systems of bad hackers with malware
- Use the tools to take over the control on Hackers systems to destroy it
What is State/National Sponsored Hacking
State/National Sponsored Hacking is the legal hacking done by the hackers working under the government to secure their data. They also do cyberattacks on other country servers and systems for the purpose of their own safety. These state/National sponsored hackers have licensed hackers and they won’t be caught by the police while using hacks being in their own country. They have all the access to the resources required for hacking and can use any kind of tool.
State/National Sponsored Hackers works under the government or organization to secure its information from attacks and get the information about the cyberattacks before it takes place.
What is Hacktivism
Hacktivism is the activity of misusing the computer system and servers for political, religious, and socially motivated reasons. The hackers who perform hacktivism are known as Hacktivists. Hacktivists use hacking skills not only for their personal intentions but also for group intentions. This is a non-violate digital activity done for the gain of justice for a group cause. Making the website overload, crashing the site, leaking confidential and sensitive information is part of Hacktivism activity.
The attacks or tools used by a Hacktivist are DDoS attacks, Doxxing, and Defacement.
What is Whistleblower
The person who could be an employee of a company or a government agency, disclosing the information to the public or to the authority of their respective company or organization about illegal activities like corruption, fraud, etc., Before taking Whistleblowers into the company, they have to go through some separate laws and agreements and it allows the company to protect the Whistleblowers from losing their job. Also, they have an option to file an allegation or complaint to the higher authorities against a company or an individual department.
These Whistleblowers are of two types. They are
Internal Whistleblowers
The Whistleblowers who report the illegal activities to the senior or higher authorities of an organization or a company are known as Internal whistleblowers.
External Whistleblowers
The External Whistleblowers are the type of whistleblowers who reveal their wrongdoings to the people outside the organization like media, higher government officials, etc.
How to become a professional ethical hacker
Before going to become an ethical hacker, you need to know all the details related to the course, certification exam, job roles and also decide the area you want to work in. Just follow the below steps to know how to become a professional ethical hacker.
Step 1: Know about the types of hackers
First, you need to know about the types of hackers and their opportunities. There are a lot of jobs available in the government sector, banks, military, and some private organizations.
Step 2: Select the area that you want to work
Select the area where you want to work primarily with hardware or software and analyze the basic requirements to become a professional in that area. Its also better to get the basic knowledge of both the hardware and software areas. You should know all the components and functions of the system on which you want to work.
Step 3: Learn about LINUX OS
LINUX is an open-source operating system that offers strong security for the device. It is the best OS used for hacking and it also provides sample tools for hackers. So, you need to know about LINUX OS without skipping.
Step 4: Learn Programming languages
As a hacker, you need to learn the most basic C programming language including C++, Python, Java, and more. Mostly the hackers use the python language to hack devices or any software. So, better to get a grip on the Python language. Including these programing languages it better to know the Encryption and decryption. Encryption helps to secure the data, and it is also important to remove the encryption of some data, passwords, and more.
Step 5: Learn the best hacking course
There are a wide variety of courses available in Ethical hacking. Select the one you want and gain the knowledge in that course and become a professional hacker. You can get premium and free courses in the next sections of this tutorial.
Step 6: Know About Network
Hacking is all about playing with networks. So, it is more important to learn the Network concepts like how they are created and protected. You should have a basic knowledge of Networking, types, protocols, and more. The knowledge of these concepts is beneficial to hack the device through the network easily.
Step 7: Vulnerabilities
Search for Vulnerabilities by scanning the system or network because these are the loopholes of a system that are responsible for easy hacking. Create vulnerabilities on your own and observe how they are affecting the system.
Step 8: Make experiments and practice on your own
After learning the bit of information, it’s better to work on it to know what actually happens. Keep on practicing in various environments. Make experiments on the hardware and software of the device to get control of the device and protect the device from hacking.
Step 9: Get certified
Take a test C|EH test and get a certificate as an ethical hacker. It would help you succeed in your profession.
Step 10: Connect with other hackers
Finally, the most important thing you want to do is always stay connected with the hacker community. It helps you gain more knowledge by exchanging and share information and you can also work as a team.
Top Ethical Hacking Courses for Cyber Security Professionals
Video Tutorial
We Provided this article in the form of a Video Tutorial for our reader’s convenience. If you are interested in reading, skip the video for now and watch it after the completion of reading this article.
1.Learn Ethical Hacking From Scratch: Udemy
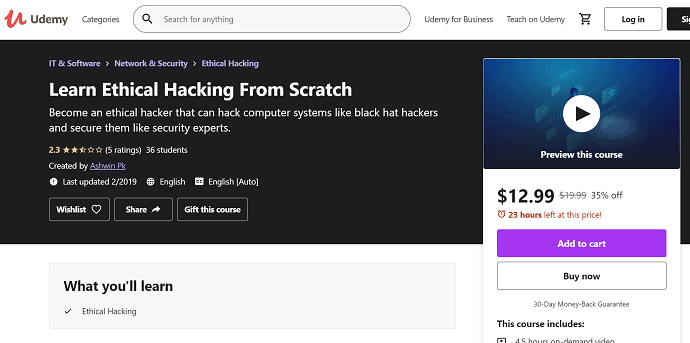
This Ethical hacking training course is offered by Udemy. It covers everything about penetration testing, hacking, and other related topics. The course is designed for new entrants. It focuses on practical approaches of the study and provides insights into the communication among devices on the same network. This course will help you to learn Ethical hacking from scratch.
Level: Beginner
Rating: 4.5
Duration: 14.5 Hours (approximately)
2.LinkedIn Learning- Ethical Hacking Training Course – Lynda
LinkedIn is hands down the best platform available for individuals to grow in their professional careers. LinkedIn Learning is also one of the best and most favorite among professionals when it comes to ethical hacking courses and hacking training.
Level: Intermediate-Advanced
Rating: 4.5
Duration: 6 weeks / 5-6 hours weekly (approximately)
3.Cybersecurity Specialization – Coursera
The specialization in cybersecurity is a level above the basic certifications. This Cybersecurity Specialization course from Coursera is recommended to individuals already within the cybersecurity industry looking to upscale their skill set. The course covers significant issues like secure systems and interactions leveraging cryptography.
Level: Intermediate
Rating: 4.4
Duration: 8 months/2 hours per week (approximately)
4.Penetration Testing and Ethical Hacking Training Course
Leo Dregier is a well-known name in the ethical hacking scene. The cybersecurity expert has created the complete penetration testing course which comes in 19 modules. The course is designed for professionals who are already in the field as well as for people who are just starting.
Level: Beginner-Advanced
Rating: 4.5
Duration: 23 hours (approximately)
5.The Complete Ethical Hacker Certification Exam Prep Course
This course is also offered by Udemy.com. This is very elemental for the ethical hacking certification tests. The 16.5-hour course covers core topics that are key to cybersecurity. However, the course demands familiarity with intrusion detection systems, firewalls, antiviruses, and other basic security jargon.
Level: Intermediate-Advanced
Rating: 4.3
Duration: 16.5 hours (approximately)
6.The Complete Ethical Hacking Course: Beginner to Advanced
This course is also one of the flagship Udemy ethical hacking courses. The course has been curated by the veteran ethical hacking expert- Ermin Kreponic. Since the 24-hour course is being delivered by the leader of the industry himself, it is short, crisp, and to the point.
Level: Beginner-Advanced
Rating: 4.3
Duration: 24.5 hours (approximately)
7. Cybersecurity For Managers: A Playbook
When it comes to learning, why not learn from the best in the field! The course has been introduced by industry experts from the Massachusetts Institute of Technology. It includes cybersecurity risk management, practical implications of privacy offsets, and cybersecurity management approaches along with other key elements.
Level: Beginner-Advanced
Rating: 4.5
Duration: 23 hours (approximately)
8.Cyber Security Basics: A Hands-on Approach
The certified ethical hacker certification Hands-On Approach course is offered by the Universidad Carlos III de Madrid. The course also trains students on the prevalent cybersecurity threats that plague the world. This makes it one of the hottest choices among candidates.
Level: Intermediate
Rating: 4.5
Duration: 6 weeks / 5-7 hours per week (approximately)
9.Specialization in Hacking For Beginners
The mentioned course is offered by reputed hackers in the ethical hacking industry. Through its problem-centric approach and discrete learning, the course has been a hit among the students. If you seek to gain maximum in the minimum time possible, you should check out this course.
Level: Beginner
Rating: 4.5
Duration: 2.5 Hours (approximately)
10.Hacking and Patching Course
Hacking and Patching course is the most massive open online course when it comes to ethical hacking. It is ideal for learners who are interested in the command injection technique. The hacking and Patching course also teaches students about Linux system depositing, hiding trojans, security design patterns, and more.
Level: Intermediate
Rating: 3.9
Duration: 17 Hours (approximately)
5 Free Ethical Hacking and Cyber Security Courses Online
1. Ethical Hacking with Hak5 Device – Udemy
Ethical Hacking with the Hak5 device is the free hacking course available in Udemy. This course helps you to learn about the USB Rubber Ducky, the O.MG cable, and more. You can also get complete information about the importance of physical security and the reasons for not connecting the unknown external devices.
Level: Beginner
Rating: 4.7
Duration: 1hr 7 Min (approximately)
2. Ethical Hacking – SQL Injection Attack – Udemy
Ethical Hacking – SQL Injection Attack is a free online Ethical hacking course provided by Udemy. This provides the information to learn how a website gets attacked and hacked by the Injection attacks – Database Penetration testing. After the completion of this course, you will be able to use kali Linux database Penetration testing tools and also can perform SQL injection attacks.
Level: Beginner
Rating: 4.5
Duration: 57 Minutes (approximate)
3. Ethical Hacker – Alison
Ethical Hacker is a free online course that helps you to learn the basics of being an ethical hacker, and cybersecurity for systems and networks with this ethical hack. You can also learn about reconnaissance, protocols, Windows Hacking, attacking Web technologies, and pen testing wireless networks.
Level: Beginner
Rating: 5
Duration: 5-6 Hours (approximate)
4. Introduction to Ethical Hacking – Great Learning
Introduction to Ethical Hacking by Great Learning is a free online course about Ethical Hacking( White Hat Hacking). In the present scenario, most organizations and companies are looking for Ethical Hackers to secure their confidential and sensitive data from attacks. This course helps you to learn about the fundamentals, processes, outcomes of Ethical Hacking.
Level: Beginner
Rating: 4.48
Duration: 2.5 Hours of Video content (approximate)
5. Introduction to IT & Cybersecurity – Cybrary
Introduction to IT & Cybersecurity is a free online course provided by Cybrary to gain knowledge and learn about the basic things that are necessary. Through this course, you are able to learn about several cybersecurity toles like Network Administrator, Incident Responder, System Administrator (SysAdmin), Penetration tester, Cloud Engineer, Cybersecurity Manager, and Privacy Analyst.
Level: Beginner
Rating: 4.4
Duration: 1Hr 41 Min (approximate)
Best Ethical Hacking Courses for Cyber Security Professionals – FAQs
Is hacking a good Career?
Yes, it is a good career if you are interested in ethical hacking and cyber security field but it requires a great knowledge of the whole IT field.
Does hacking require coding?
Programming skills and SQL skills are essential to becoming an effective hacker.
What type of hacking is illegal?
When a hacker try to breach a system without authorization, it is considered as unlawful. These kinds of hackers are called as Black Hat Hackers.
What language do Hackers use?
Python is the language used by Hackers. Since Python is so widely used by hackers, there is a host of different attack vectors to take into considerations.
