A decade or two ago, cybercrime felt like a distant concept often depicted in cinematic fiction and predominantly impacting large corporations. Fast forward to the present day, cybercrime is so prevalent it’s no longer a “Big business problem,” as 43% of victims are small and medium-sized businesses.
With an alarming estimate of over 8 00,000 cyber-attacks reported annually, businesses must prioritize robust cybersecurity measures to thrive in this digital era. But given the intricate nature of cyber security, where should one start? We’ve shortlisted key cyber security practices every business owner should implement in this article as a starting point to preventing cybercrime.
- RELATED – 4 Great Ways to Get Serious on Cybersecurity
- 10 Cybersecurity Tips for Individuals and Students
Cybersecurity Practices Every Business Owner Should Implement
Back-Up Business Data and Invest in Cloud Security

Cybercriminals are continuously evolving their tactics. They’re becoming increasingly innovative, using advanced malware and tactics like zero-day vulnerabilities to bypass robust cyber security measures. Thanks to technologies like Deepfake, these criminals can now create compelling videos and audio to impersonate you or your employees, thus gaining access to your systems. Deepfake content can also be used for disinformation campaigns and even fraud.
This ever-evolving nature of cybercrime only means one thing: even when you employ the best cyber security tactics, there’s always a looming risk of cyber-attacks. It’s thus prudent to implement data backup solutions to ensure the recovery of critical information in the event of a cyber-attack or data loss.
A data backup also means you can still safely access your data even during a ransomware attack where hackers encrypt your systems, thus thwarting their ransom-request attempts. In addition to data backups, implement a disaster recovery plan and invest in Cisco cloud security.
Train Your Employees
While your employees constitute one of your most valuable assets, they can unintentionally become a liability to your enterprise’s cyber security. For example, your employee might unintentionally share sensitive information through unencrypted emails, exposing confidential data to potential cyber criminals.
Similarly, employees lacking familiarity with cyber security practices may inadvertently misconfigure security settings on corporate software or devices, creating system vulnerabilities. Employees may innocently fall for phishing emails, compromising the integrity of your network and data. Statistics reveal the average employee encounters 14 phishing attempts annually, with a distressing one in three employees falling prey to these deceptive lures.
Investing in employee cyber security training is thus the first and most critical step to mitigating cybercrime risks. Training equips your team with the knowledge and skills to effectively recognize and thwart cybercrime scams. In addition to heightened awareness, educated employees often adhere to proper cyber security protocols, reducing the likelihood of employee-fueled cyber-attacks while strengthening a business’s overall cyber resilience.
Update Your IT Infrastructure

Cybercriminals always look for the slightest weakness they can exploit to get into business systems. It’s important to regularly update your IT systems to protect your business.
System updates often feature strong security patches that eliminate bugs and potential vulnerabilities a hacker might exploit to gain system access. They also often come with built-in security features like multi-factor authentication, making it difficult for hackers to penetrate your IT infrastructure. Keeping your computer systems up to date helps you prevent costly downtimes your business might have experienced if an attack is successful.
Plan for Mobile Devices

While mobile devices, for instance, laptops and smartphones, promote remote work and productivity, they also present a potential entry point into your network. Hackers may use a remote worker’s malicious or poorly coded apps to compromise the device’s security and steal data. Besides apps, remote workers frequently connect to public WIFI networks, which may lack security, exposing your business to attacks like man-in-the-middle and eavesdropping.
These devices are also always at risk of being misplaced or stolen, and if they aren’t adequately protected, sensitive company data can be accessed by unauthorized individuals. In other instances, the employee may inadvertently leak company data from these mobile devices through file sharing or cloud backups. Thus, it’s incredibly imperative for businesses with BYOD and remote-work arrangements to implement mobile security strategies. This includes enforcing strong security policies, encouraging employees to update devices and apps regularly, and employing mobile device management solutions. Taking such steps allows your business to leverage the perks of policies like BYOD without compromising cyber security.
Navigating the Ever-Evolving Cyber Security Landscape
The cybercrime landscape has been through a dramatic transformation in the past decade. What was once considered a distant threat is now a pervasive menace that spares no business, whether small or large. While no cyber security strategy can guarantee complete immunity, implementing the above fundamental practices will significantly enhance your system security. Data backups ensure data recovery and render ransomware extortion attempts futile, while employee cyber security training reduces the risk of employee-induced security breaches. Also, invest in cloud security to keep your data backups safe.
Use ManageEngine Endpoint Central

ManageEngine Endpoint Central is a cutting-edge Unified Endpoint Management and Security (UEMS) solution designed to streamline and safeguard the modern-day digital workspace distributed across different device types and operating systems. The solution employs a single lightweight agent, providing comprehensive device lifecycle management and robust security functionalities like real-time threat detection and containment mechanisms.
With a wide array of features ranging from automated patching to instantaneous endpoint analytics, the solution helps minimize operational disruptions and enhance end-user experience by addressing the need for unified management of devices, applications, and data. Integrated security capabilities like next-gen antivirus, anti-ransomware, vulnerability assessment, endpoint encryption, and web filtering further help organizations enhance the overall security posture of their endpoints.
Available in both on-premises and cloud, it seamlessly integrates into existing frameworks, offering flexibility in deployment options while facilitating interoperability and smooth functionality within diverse organizational setups.
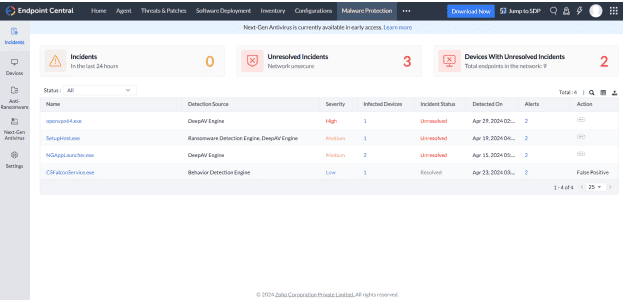
Pricing:
Endpoint Central provides flexible pricing options, starting at just $795 per year, and includes a 30-day free trial to get you started.
I hope this tutorial helped you to know about the “Cybersecurity Practices Every Business Owner Should Implement”. If you want to say anything, let us know through the comment sections. If you like this article, please share it and follow WhatVwant on Facebook, Twitter, and YouTube for more Technical tips.
- RELATED – 4 Must Know VPN uses: How to get the most out of your VPN
- What are the Advantages of VPN for PC? How is it Better than a Browser VPN?
Cybersecurity Practices Every Business Owner Should Implement – FAQs
What are the best practices of the Cybersecurity industry?
Using Strong passwords, updating your software, thinking before you click on suspicious links, and turning on multi-factor authentication are the basics of what we call “cyber hygiene” and will drastically improve your online safety.
What is the business need for cybersecurity?
Cybersecurity can disrupt your business operations, causing downtime and loss of productivity. Ensuring that your company has a robust cybersecurity strategy in place helps maintain the continuity of your operations and minimizes the potential for costly interruptions.
What are the 5 essential elements of cybersecurity?
The 5 Key elements of a Modern Cybersecurity Framework are Identify, Protect, Detect, Respond, and Recover.
What is cybersecurity practice?
Cybersecurity is the practice of protecting critical systems and sensitive information from digital attacks.
Why do we need to implement cybersecurity?
Cybersecurity is crucial because it safeguards all types of data against theft and loss. Sensitive data, protected health information (PHI), personally identified information (PII), intellectual property, personal information, data, and government and business information systems are all included.
