Do you want to know the most common types of malware and how to avoid them? Then read this article to know the most common malware types and the methods to protect you from them.
We all know about the worms and trojans that seriously mess up with our system CPU and other programs. However, there is an increased number of new threats that appear every day, and they transform into something that usually goes unnoticed for the bare eye. Some types of malware may remain unnoticed until it is too late.
The first advice on the matter would be to read professional reviews and articles for antivirus solutions that can protect you from unwanted intrusion in your life. For instance, Bitdefender free review or any other review will provide you with excessive information about what AV solution fights the best, what are the pitfalls and vulnerabilities of this software, and how to pick up the best solution.
Here we will review several most common and typical malware that you must avoid at any cost, and an AV solution will be the first measure to shield you from it.
The Most Common Types of Malware and How to Avoid Them
1.Rootkit
Rootkits are a type of malware that allows hackers to access or control your computer remotely without your notice or even without notice of your security programs. Once installed, the rootkit will enable hackers to execute files, modify system configurations, alter software, implement other types of malware, or control the computer as a part of a botnet. It is quite hard to detect rootkits, and it requires to indicate suspicious activities of your computer, signature scanning, and storage dump analysis.
Solution: along with installing antivirus, you can protect your computer by avoiding suspicious resources and downloads and regularly scanning your software for vulnerabilities.
2.Spyware
Spyware collects all user activities without notice, including activity monitoring, collection of keystrokes, search history, data harvesting, and other types of activities. Spyware can modify your browser settings and interfere with network connections. Undetected spyware can cost you your user credentials, and unwanted pop-ups or websites opened without your consent.
Solution: you can avoid spyware by updating your system and performing regular scans, as it can be spread by exploiting software vulnerabilities.
3.Ransomware

Ransomware is pretty self-explanatory, as it captures the system while demanding the ransom. It restricts your access to the files by encrypting them on the hard drive or locking down the system while showing instructions with payment demands to regain access. Ransomware threats also steal your data, and it is unlikely that you can avoid unpleasant consequences even after paying to hackers.
Solution: to avoid ransomware, scan your system regularly, use secure network connections, and avoid suspicious downloads.
4.Adware
Adware is one of the most annoying types of malware. It usually has a form of pop-up ads on websites and exploits the clicks, profiting advertisers and servers. Often they are the least harmful for you and your computer, but sometimes it can come bundled with spyware when your activity becomes tracked down and transferred to third parties.
Solution: adware can be avoided with firewalls and VPNs, avoid clicking on pop-ups on websites, or installing unknown software by mistake.
- Related: 2 Simple methods to remove Adware from your PC and browsers
- 10 Best top VPN services to Use
5.Worms, viruses, trojans
Computer worms cause the most harm to their host networks by consuming bandwidth and overloading servers; they also contain “payloads” that damage host computers. At the same time, worms can steal information, delete files, create botnets, and randomly mess up with your computer CPU. They are spread by self-replication as soon as they enter the computer system by network vulnerabilities.
Viruses are used to steal information, harm host computers, and mess up with networks, render advertisements, and cause many other harmful consequences. Viruses rely on human activity to spread, by running a program, opening a file, and others.
Trojans are the malware that uses disguise, so when you try to install legit software, the malware comes as a surprise to you. Trojans can give hackers remote access to your files, data, and allow other malicious software to affect the system (modifying files, monitor user activity), and mess up with computer performance.
Solution: Update your antivirus and avoid suspicious downloads, unsecured networks, and using USBs without repercussions.
6.Bots
Often bots are used for harmless purposes, still raising some questions about the ethics of using them for online contests or video gaming; they can also be used for malicious purposes. They can be the part of botnets, the collections of computers controlled remotely by hackers for DDoS attacks, as spambots that deliver ads on websites, or web spiders that gather server data. Often when you see CAPTCHA tests, they serve as a shield against these bots.
The usual routines – avoid suspicious software and scan your computer for vulnerabilities.
7.Use ManageEngine Endpoint Central

ManageEngine Endpoint Central is a cutting-edge Unified Endpoint Management and Security (UEMS) solution designed to streamline and safeguard the modern-day digital workspace distributed across different device types and operating systems. The solution employs a single lightweight agent, providing comprehensive device lifecycle management and robust security functionalities like real-time threat detection and containment mechanisms.
With a wide array of features ranging from automated patching to instantaneous endpoint analytics, the solution helps minimize operational disruptions and enhance end-user experience by addressing the need for unified management of devices, applications, and data. Integrated security capabilities like next-gen antivirus, anti-ransomware, vulnerability assessment, endpoint encryption, and web filtering further help organizations enhance the overall security posture of their endpoints.
Available in both on-premises and cloud, it seamlessly integrates into existing frameworks, offering flexibility in deployment options while facilitating interoperability and smooth functionality within diverse organizational setups.
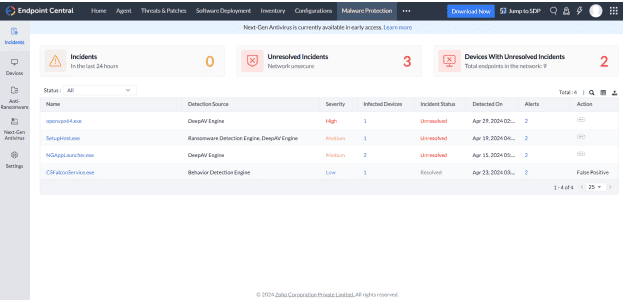
Pricing:
Endpoint Central provides flexible pricing options, starting at just $795 per year, and includes a 30-day free trial to get you started.
If you like this tutorial about the most common types of malware, please share this article and follow WhatVwant on Facebook, Twitter, and YouTube for more tips.
The Most Common Types of Malware and How to Avoid Them-FAQ
What are the most common types of malware?
Rootkit, spyware, virus, Worms, Randsomware, etc are the most common types of Malwares.
How to avoid Randsomeware?
To avoid ransomware, scan your system regularly, use secure network connections, and avoid suspicious downloads.
What is Adware?
Adware is one of the most annoying types of malware. It usually has a form of pop-up ads on websites and exploits the clicks, profiting advertisers and servers.